Shanghai ZENTEK Co., Ltd. ZENTEK 信弘,智能,信弘智能科技 Elite Partner,Omniverse,智能科技 NVIDIA GPU,NVIDIA vGPU,TESLA,QUADRO,AI, AI Training,AI Courses,Artificial Intelligence (AI),Solutions,DLI,Mellanox,InfiniBand (IB),Deep Learning, NVIDIA RTX,IT,RACLE Database,ORACLE Cloud Services,Deep Learning Institute, bigdata,Big Data, Data Security & Backup,鼎甲SCUTECH CORP,High-Performance Computing (HPC),Virtual Machines (VM), Virtual Desktop Infrastructure (VDI),Virtual Desktop Infrastructure (VDI),Hardware,Software, Accelerated Computing,High-Performance Computing (HPC),Supercomputing,Servers,Virtual Servers, IT Consulting,IT System Planning, Application Deployment,System Integration
Are you facing similar challenges in your business applications?
Difficult to Defend Against Ransomware Attacks
Ransomware variants are evolving rapidly with diverse infiltration methods. They exploit unknown vulnerabilities to infect business systems, resulting in critical data loss or forcing organizations to pay ransoms.
Limited Features, Forced Reinvestment
Businesses often buy products based on current needs. As operations evolve, existing products lack functionality or compatibility with new or upgraded systems—forcing costly reinvestment in new solutions.
Too Many Similar Products, Hard to Choose
The market is flooded with data security products of varying quality and inconsistent technical maturity. Many suffer from poor compatibility, incomplete functionality, and unstable performance.
Complex Maintenance, Difficult Management
With diverse business types and varying data security levels, multiple software systems must be deployed to meet compliance requirements. This leads to fragmented management, inconsistent configurations, and reduced operational efficiency.
Short Maintenance Cycles, Poor Service Support
To minimize upfront costs, many organizations purchase only one-year software maintenance, while hardware support is often provided by non-OEM vendors. When issues arise later, the prolonged resolution cycle magnifies data security risks.
Challenges in Business Compliance Management
With the enforcement of laws such as the Cybersecurity Law, Classified Protection 2.0, Data Security Law, and Cryptography Regulations for Critical Infrastructure, organizations face stricter requirements for data security governance.
InfoKist Disaster Recovery & Backup Appliance
Integrates DBackup enterprise-grade backup and recovery software with high-quality, optimized hardware. This all-in-one solution combines backup, disaster recovery, data copy management, and database replication, delivering robust performance and reliability.
Core Advantages
The Final Line of Defense Against Ransomware
Built on Dingjia’s comprehensive anti-ransomware architecture, the solution not only safeguards the backup system itself from ransomware attacks but also enables rapid and reliable data recovery after business applications are infected.
MFA Multi-Factor Authentication
Since ransomware and hackers often target system credentials, the solution supports multi-factor authentication (OTP, email, UKey) to prevent unauthorized access even in the event of password leakage.
Deduplication Technology
Leverages industry-leading multidimensional deduplication technology supporting both source-side and target-side deduplication. This significantly reduces backup storage consumption, enhances backup efficiency, and lowers overall storage costs.
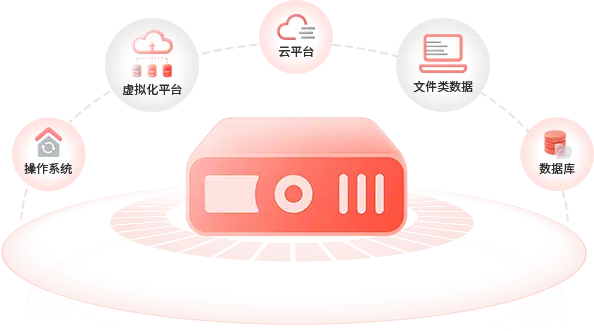
Broad Compatibility
Compatible with all mainstream CPUs and operating systems, over 95% of databases, virtualization platforms, and cloud-native environments, and continuously updated to support new versions and emerging applications.
Large-Screen Visualized Management
An integrated visualization dashboard provides real-time insights into backup task details, job status, alerts, and capacity metrics—enabling comprehensive system monitoring and proactive risk detection.
Secure and Reliable Hardware
Equipped with redundant power supplies and fans, RAID controller with power-loss protection, and RAID6 dual-disk fault tolerance. Each unit undergoes rigorous factory testing to ensure stable and secure hardware performance.
Full-Stack Domestic Architecture
Supports processors, operating systems, and trusted domestic databases certified for security and reliability. Fully compliant with the Xinchuang (information innovation) localization standards and requirements.
Certifications and Compliance
Certified under China Compulsory Certification (CCC), Cybersecurity Dedicated Product Testing & Certification, and National Information Security Product Certification, providing strong compliance assurance.
Three-Year Warranty for Software and Hardware
Both the embedded software and hardware components come with a three-year OEM warranty, ensuring long-term professional support. Renewal can be completed online, simplifying post-deployment maintenance.
Nationwide Service Coverage
Backed by a nationwide network of OEM after-sales and technical support teams, ensuring fast response for deployment, optimization, maintenance, and emergency recovery.
Application Scenarios

Manufacturing Business Data Protection
Designed for manufacturing enterprises to safeguard critical business data such as ERP, MES, and design files. Enables rapid backup and recovery to prevent production downtime caused by ransomware attacks or hardware failures.

Government Business Data Protection
Provides high-efficiency disaster recovery, compliance auditing, and automated drills for core government platforms, archive systems, and government clouds—ensuring stability, reliability, and compliance of public service operations.

Vocational and General Education Data Protection
Tailored for vocational schools and general education institutions to protect academic systems, electronic archives, and teaching resources from ransomware threats. Ensures continuous and reliable operation of educational services.

Healthcare Business Data Protection
Supports critical medical systems such as HIS, LIS, and PACS, offering minute-level data recovery, remote disaster recovery, and full compliance protection to ensure uninterrupted healthcare service continuity.
